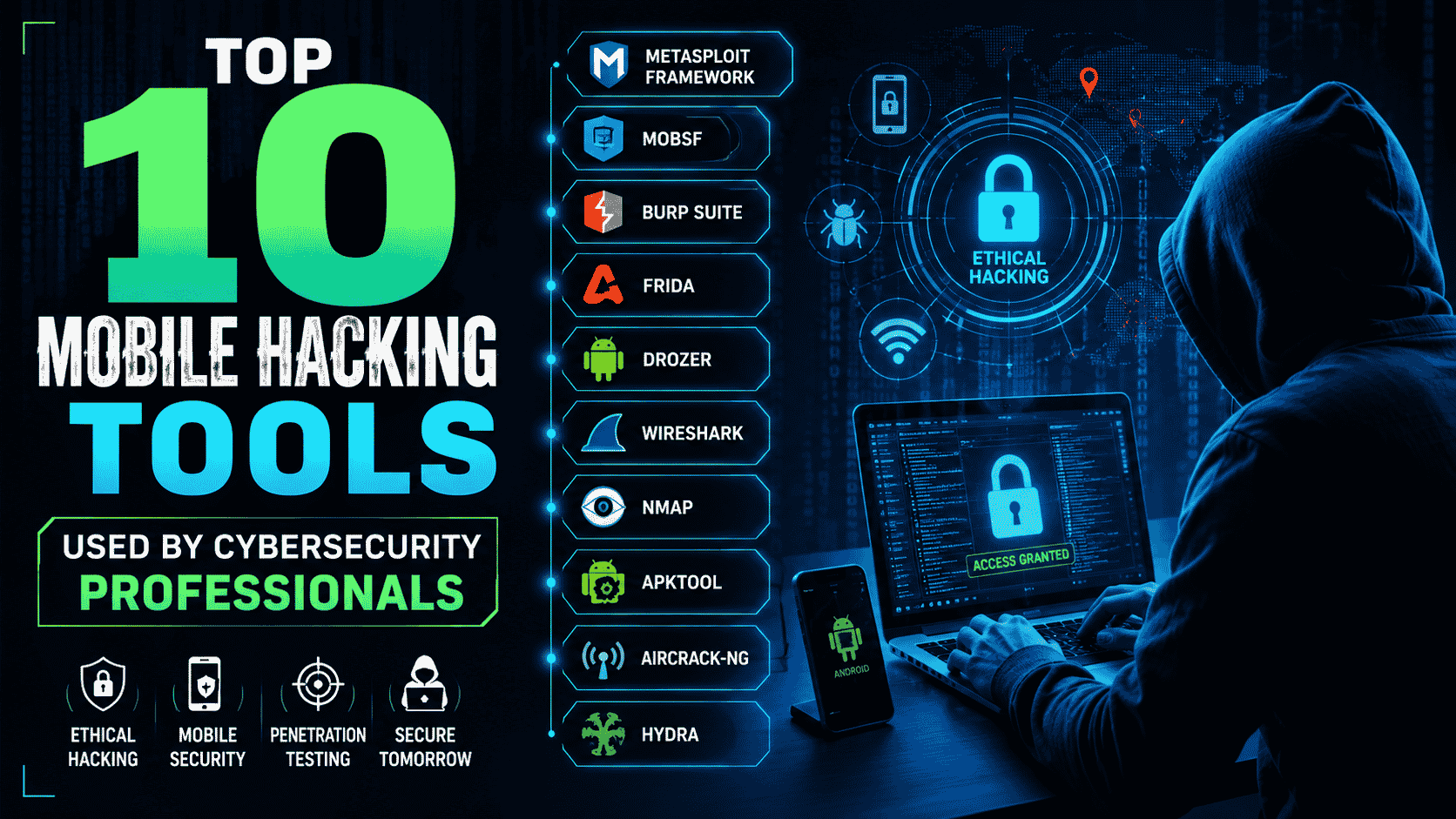
10 mobile hacking tools have shown that mobile devices have become the backbone of modern communication, banking, social networking, and business operations. As smartphone usage continues to grow rapidly, cybercriminals are increasingly targeting Android and iOS devices with sophisticated attacks. This has created a huge demand for ethical hackers and cybersecurity professionals who can identify […]
Introduction Cybersecurity Courses: Cybersecurity is one of the fastest-growing career fields in the world. Companies are not just looking for certificates—they want real, hands-on skills. If you want to build a strong career in cybersecurity, practical experience is just as important as theory. In this blog, we will explain how to get hands-on cybersecurity experience, […]
Introduction: Mobile Security Guide: Today, mobile phones have become our mini-computers. We use them for banking, chatting, e-commerce, payments, office work, OTPs, emails, and even storing personal photos and documents. This is why mobile security is now more important than PC security. Whether you are a beginner trying to understand cybersecurity or planning to Learn […]
Palo Alto Firewall Training: Palo Alto Firewall Advanced Cheat Sheet: For seasoned network security professionals, the Palo Alto Networks Next-Generation Firewall (NGFW) is the industry standard. Moving beyond basic policies and object creation requires mastering complex deployment architectures, advanced security services, and deep-level troubleshooting. This cheat sheet is specifically designed for advanced learners—those preparing for […]
10 Instagram Hacking Scams: Our services are strictly training in cybersecurity and ethical hacking. We do not hack Instagram or any social accounts. Introduction (Common Instagram Hacking Scams) Instagram is one of the most popular social media platforms in the world. With over 2 billion monthly active users, it has also become a hot target […]
Recover LinkedIn Account: 📌 Table of Contents Introduction: LinkedIn has become more than just a job-searching platform — it’s a professional network that holds valuable information, contacts, and business opportunities. Unfortunately, hackers often target LinkedIn accounts to steal personal data, scam connections, or spread malicious links. If your account has been compromised, the first step […]
Recover Hacked Instagram Account: Our services are strictly training in cybersecurity and ethical hacking. We do not hack Instagram or any social accounts. Learn How To Recover Hacked Instagram: Instagram is one of the most popular social media platforms, but it is also a prime target for hackers. If your account gets hacked, it can […]
Instagram Account Hack Proof: Our services are strictly training in cybersecurity and ethical hacking. We do not hack Instagram or any social accounts. Keep your Instagram safe from hackers! Instagram is one of the most popular social media platforms, which makes it a big target for hackers. From phishing links to brute-force attacks, cybercriminals use […]
Social Media Account Hacked: From Axximum Infosolutions – Cybersecurity Experts Have you ever tried logging in to your social media account, only to find that your password no longer works? If hackers have taken over your Facebook, Instagram, Twitter (X), YouTube, or LinkedIn account, it can feel scary and frustrating. But don’t panic — there […]
How to Report a Hacked Instagram: Recover a Hacked Instagram account: Instagram is one of the most popular social media platforms worldwide. But in 2025, cybercriminals are smarter than ever, and hacked Instagram accounts are becoming common. If your account is hacked, you may lose access, your followers might receive spam, and your private data […]